KMSPico | Activator Windows&Office | 2025
About KMSPico
KMSPico is a multifunctional activation tool created to help users register Windows and Office products. Unlike many traditional activators, it provides an automated system that seamlessly integrates activation keys into your operating system. This ease of use and high efficiency make it stand out among other tools.
Supported Versions of Windows & Office
| Product | Version |
|---|---|
| Windows | 7, 8, 8.1, 10, 11 |
| Office | 2010, 2013, 2016, 2019, 2021 |
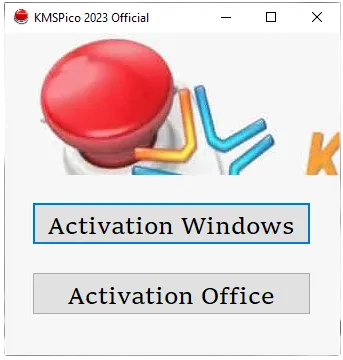
How to Use KMSPico?
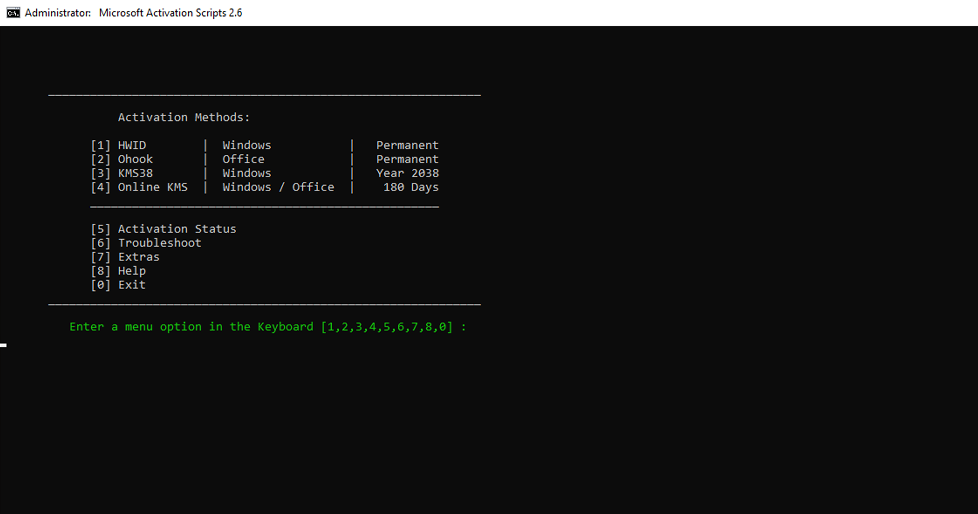
KMSPico stands out due to its user-centric design and reliable performance. If this tutorial was beneficial, feel free to share your feedback to assist other users.
Frequently Asked Questions (F.A.Q.)
Is KMSPico safe to use?
Yes, when obtained from a reputable source, KMSPico is safe. However, always exercise caution by ensuring your download is from a verified provider.
Does KMSPico support all editions of Windows?
Indeed, it supports a wide range of Windows versions, including Windows 7, 8, 8.1, 10, and 11.
Can I activate Office using KMSPico?
Yes, KMSPico works seamlessly with Microsoft Office editions from 2010 through 2021.
Is using KMSPico illegal?
Using KMSpico is completely legal if you use it for educational purposes.
Why does my antivirus flag KMSPico?
Due to its nature of modifying system files for activation, many antivirus programs detect KMSPico as a potentially unwanted application (PUA).
Conclusion
This guide aimed to provide a thorough understanding of KMSPico and its functionalities. Additionally, users might consider KMSAuto, another tool designed for simplified activation processes.
Despite the fact that KMSpico offers an effective solution for activating Microsoft products. We recommend purchasing only licensed products.